The 19 Primitives
Named patterns for governed agentic systems — runtime, lifecycle, and substrate primitives organized into the Rings Model.
The 19 primitives are the building blocks of AGF. They are not new inventions — they are named patterns drawn from established practice across distributed systems, security engineering, compliance, and control theory. The contribution is pulling them together into a composable architecture for the agentic context.
Runtime Primitives (#1–#17)
These operate within or across the ring pipeline during agent execution.
| # | Primitive | Ring | One-Line Description |
|---|---|---|---|
| 1 | Separation of Producer & Verifier | 0+1 | The agent that creates output must not be the sole agent that validates it |
| 2 | Validation Loops with Convergence Gates | 1 | Iterative verification until quality thresholds are met or budget is exhausted |
| 3 | Self-Improving Cycles | 3 | The system gets better by learning from its own execution |
| 4 | Adversarial Critique | 1 | Dedicated challenger that actively tries to find flaws |
| 5 | Structured Output Persistence | Fabric | Every ring produces and consumes structured artifacts — the data contract |
| 6 | Provenance Chains | Fabric | Every output carries its full decision history |
| 7 | Bounded Agency | 2 | Agents operate within explicit, enforced boundaries |
| 8 | Governance Gates | 2 | Explicit decision points where execution pauses for authorization |
| 9 | Policy as Code | 2 | Governance rules as versioned, executable, testable objects |
| 10 | Event-Driven Observability | Fabric | Every ring emits structured events — the shared nervous system |
| 11 | Trust Ladders | 2+3 | Trust is earned through demonstrated performance, not granted by default |
| 12 | Memory-Augmented Reasoning | 0+3 | Agents reason with persistent memory, not just immediate context |
| 13 | Error Handling & Recovery | Fabric | Graceful degradation, checkpointing, compensation |
| 14 | Identity & Attribution | Fabric | Every agent has authenticated, inspectable identity |
| 15 | Adversarial Robustness | Security | Assume breach. Defense in depth. Verify explicitly. |
| 16 | Transaction & Side-Effect Control | 0+2 | Pre-commit/commit/post-commit for irreversible actions |
| 17 | Data Governance & Confidentiality | 2+Fabric | Classification, consent, PII, lineage, retention at every data flow |
Lifecycle Primitive (#18)
| # | Primitive | Scope | One-Line Description |
|---|---|---|---|
| 18 | Evaluation & Assurance | Pre-deployment | The gate before the gate — validates configurations before they reach production |
Substrate Primitive (#19)
| # | Primitive | Scope | One-Line Description |
|---|---|---|---|
| 19 | Agent Environment Governance | All rings | Governed composition of context, instructions, tools, workspace, and memory |
How They Map to the Rings
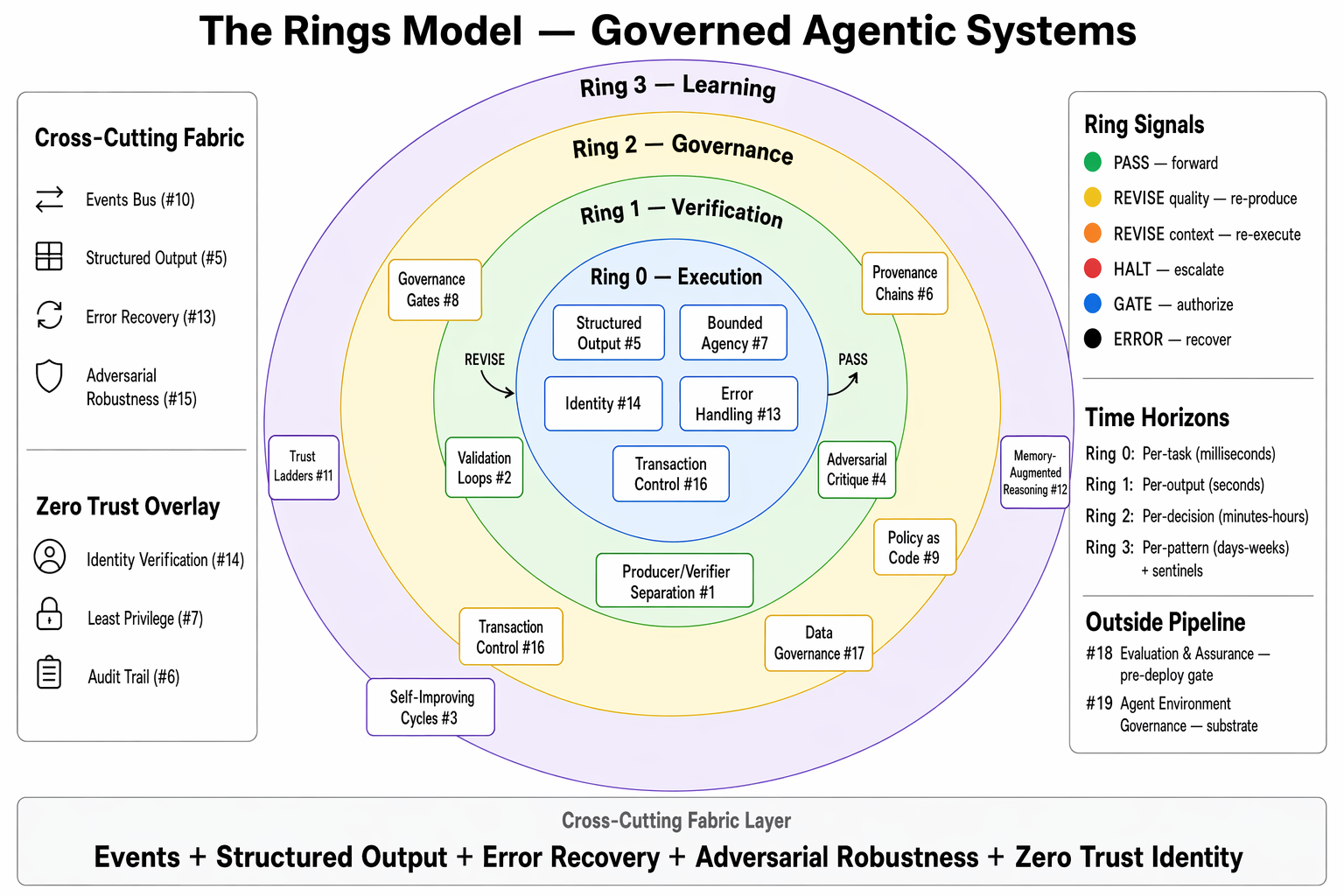
- Ring 0 (Execution): #1, #5, #12, #14, #16 — the agent works, produces structured output, with identity
- Ring 1 (Verification): #1, #2, #4 — separate verifier, iterative loops, adversarial critique
- Ring 2 (Governance): #7, #8, #9, #11, #16, #17 — boundaries, gates, policy, trust, transactions, data governance
- Ring 3 (Learning): #3, #11, #12 — self-improvement, trust calibration, memory
- Fabric: #5, #6, #10, #13, #14, #17 — structured output, provenance, events, errors, identity, data governance
- Security: #15 — adversarial robustness as a pervasive concern
Primitive Interaction Tensions
The primitives are not always harmonious. AGF names seven tensions with architectural invariants that resolve them:
| Tension | Conflict | Invariant |
|---|---|---|
| Self-Improvement vs. Reproducibility | #3 changes behavior; #6 requires traceability | Always reproducible at a specific version |
| Trust Ladders vs. Governance Gates | #11 reduces oversight; #8 ensures accountability | Can skip a spot-check, never regulatory approval |
| Bounded Agency vs. Self-Improvement | #7 constrains; #3 improves — can it expand itself? | The box can get smarter inside. It cannot grow itself. |
| Validation vs. Latency/Cost | #2 improves quality; each pass costs time and money | Quality bounded by economics, not just capability |
| Memory vs. Signal-to-Noise | #12 accumulates knowledge; stale memories inject noise | Growth without curation is hoarding, not learning |
| Policy as Code vs. Self-Improvement | Can Ring 3 change Ring 2's policy rules? | Can suggest governance changes, cannot enact them |
| Environment vs. Governance Integrity | #19 optimizes the environment — but it IS the control surface | The environment can get better. It cannot get less governed. |
Gate Vocabulary & Governance Decision Records
AGF's gate-related concepts form a four-part vocabulary — not alternative spellings of one concept. See DECISIONS.md #8 for the full disambiguation.
- Ring Control Signals (
PASS / REVISE / HALT / GATE / DELEGATE / ERROR) — how primitives in adjacent rings signal each other via the Composability Interface. Emit observability events (Primitive #10), not GDRs. - Gate Resolutions (
APPROVE / REJECT / MODIFY / DEFER / ESCALATE) — the Primitive #8 enum returned by an authorizer when a gate fires; also the return value of theGATERing Control Signal. Emit a Governance Decision Record (GDR). - Domain Outcomes — domain-specific gate decision enums (e.g., Tool Gate's
Authorized / Conditionally Authorized / Denied) that map onto Gate Resolutions. Emit a GDR.
Every Gate Resolution and every Domain Outcome emits a Governance Decision Record — AGF's canonical audit artifact at gate boundaries. The GDR is the machine-readable companion to the human-readable rationale (dual-form principle, DECISIONS.md #5). The corresponding gate_resolved observability event references the GDR by decision_id.
Primitive Attribution
AGF's position is that the primitives are named patterns drawn from prior art, not novel inventions. The contribution is composition — pulling these patterns into a coherent architecture for the agentic context, naming their relationships, and specifying the invariants that let them work together. This table shows where each primitive's intellectual lineage sits.
| # | Primitive | Primary lineage | AGF contribution |
|---|---|---|---|
| 1 | Separation of Producer & Verifier | Distributed systems (code review, formal verification); CSA MAESTRO; NIST SP 800-53 SA-11 | Naming the producer/verifier split as a first-class agentic invariant |
| 2 | Validation Loops with Convergence Gates | Control theory; agentic research (reflection, ReAct); NIST AI RMF "Measure" | Adding explicit budget/convergence gates to the verification loop |
| 3 | Self-Improving Cycles | Reinforcement learning; MLOps continuous training; meta-learning research | Ring 3 placement + tension invariants with reproducibility and bounded agency |
| 4 | Adversarial Critique | Red teaming; OWASP Top 10 for LLM Apps; adversarial robustness research | Dedicated Ring 1 challenger role distinct from the verifier |
| 5 | Structured Output Persistence | Event sourcing; data contracts; OpenTelemetry semantic conventions | Ring-to-ring data contract as Fabric primitive |
| 6 | Provenance Chains | SLSA provenance; W3C PROV; SOC 2 / EU AI Act Art. 12 traceability | Extending provenance to agent decisions, not just artifacts |
| 7 | Bounded Agency | Capability-based security (POLA); sandboxing; NIST AC controls | Applying capability discipline to agent action surfaces |
| 8 | Governance Gates | Approval workflows; COBIT; ISO 9001; ITIL change management | Unified gate primitive + Gate Resolution enum + GDR artifact |
| 9 | Policy as Code | OPA / Rego; GitOps; NIST CSF; CSA AICM | Specifying policy-as-code as a governance-ring primitive |
| 10 | Event-Driven Observability | OpenTelemetry; SIEM practice; DORA research | Mandating event emission at every ring boundary |
| 11 | Trust Ladders | CSA ATF (Intern → Principal tiers); Microsoft AGT maturity | Cross-ring (2+3) placement tying trust to observed performance |
| 12 | Memory-Augmented Reasoning | RAG; MemGPT; vector-store research | Governance invariants over memory curation and revision |
| 13 | Error Handling & Recovery | Fault tolerance (Erlang/OTP); SAGA compensation; NIST CSF Respond/Recover | Ring-aware error contracts (Fabric primitive) |
| 14 | Identity & Attribution | SPIFFE/SPIRE; NIST SP 800-63; Non-Human Identity practice | Identity as a Fabric primitive spanning all rings |
| 15 | Adversarial Robustness | OWASP Top 10 for LLM; MITRE ATLAS; NIST AI RMF; CSA MAESTRO | Cross-cutting Security primitive with defense-in-depth invariant |
| 16 | Transaction & Side-Effect Control | Database transactions (2PC); functional purity; tool-use safety research | Pre-commit/commit/post-commit pattern for agent actions |
| 17 | Data Governance & Confidentiality | ISO 27001; NIST SP 800-53 SC/MP; GDPR; EU AI Act | Data-governance invariants at every agent data flow |
| 18 | Evaluation & Assurance | MLOps eval; FDA software assurance; HELM / BIG-bench | Pre-deployment lifecycle placement ("gate before the gate") |
| 19 | Agent Environment Governance | Container isolation; capability security; agent sandboxing research | Composed governance of context + tools + workspace + memory |
How to read the table: "Primary lineage" names the source communities or specific works that AGF draws from. "AGF contribution" names what we think is genuinely additive — usually placement, naming, or invariant specification, not new theory. Where AGF's contribution is framing or synthesis, the underlying ideas remain the intellectual property of the cited communities.
Implementation Priority
For a practical implementation roadmap organized by phase, see the AI Engineering Profile.
For the complete primitive catalog with full patterns, deployment modes, security architecture, and existing work mapping, see the canonical source.