Architecture Diagrams
Visual reference models for the AGF framework — rings, security, deployment, observability, and more.
AGF includes 24+ architecture diagrams across rings, security, deployment, observability, decision intelligence, and positioning. Key diagrams are shown below. All diagrams are available in the diagrams/ directory.
AGF in the Governance Landscape
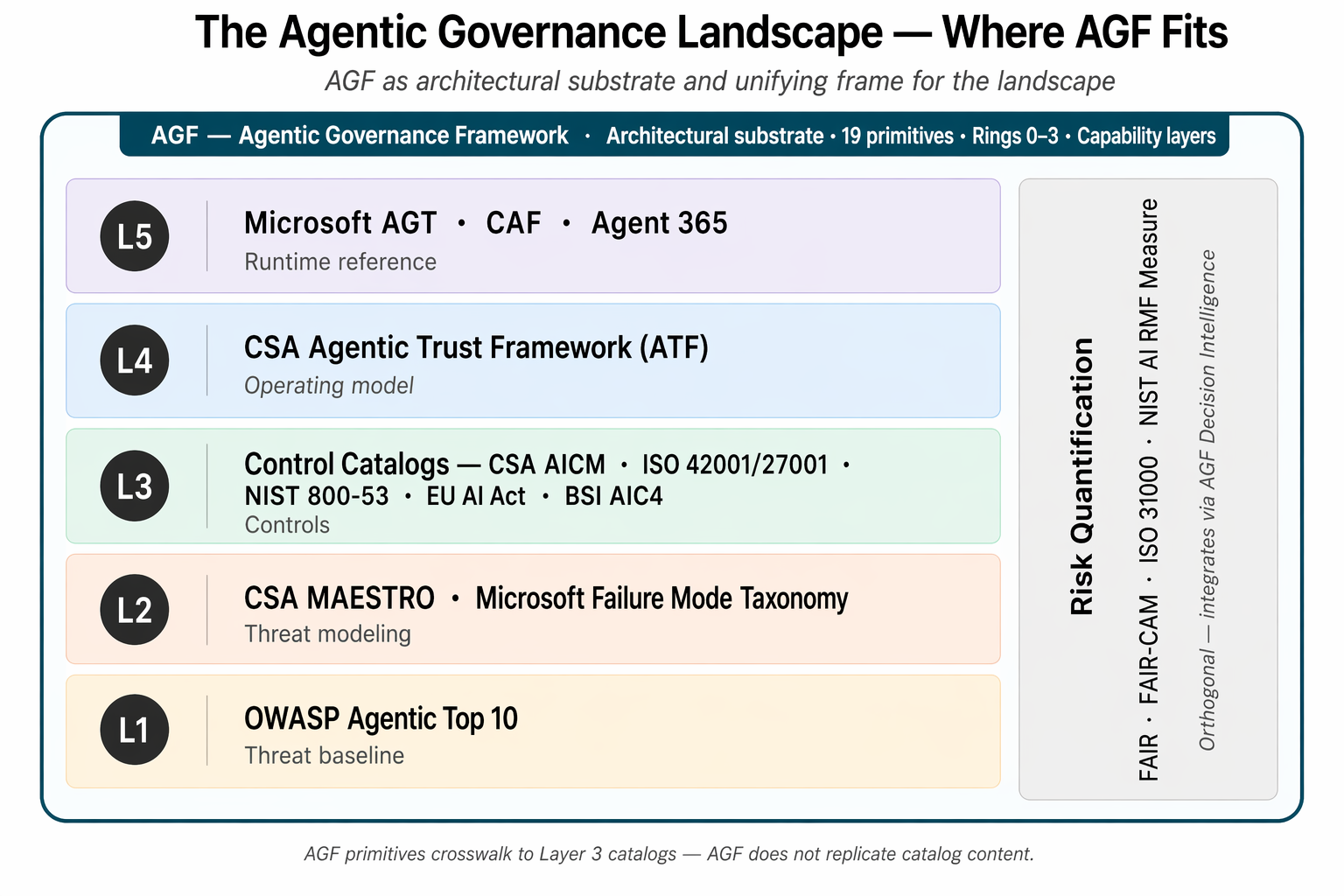
Seven-layer stack showing where AGF fits among OWASP, MAESTRO, AICM/ISO/NIST catalogs, CSA ATF, Microsoft AGT, and FAIR. Learn more
How AGF Works — Four Verbs
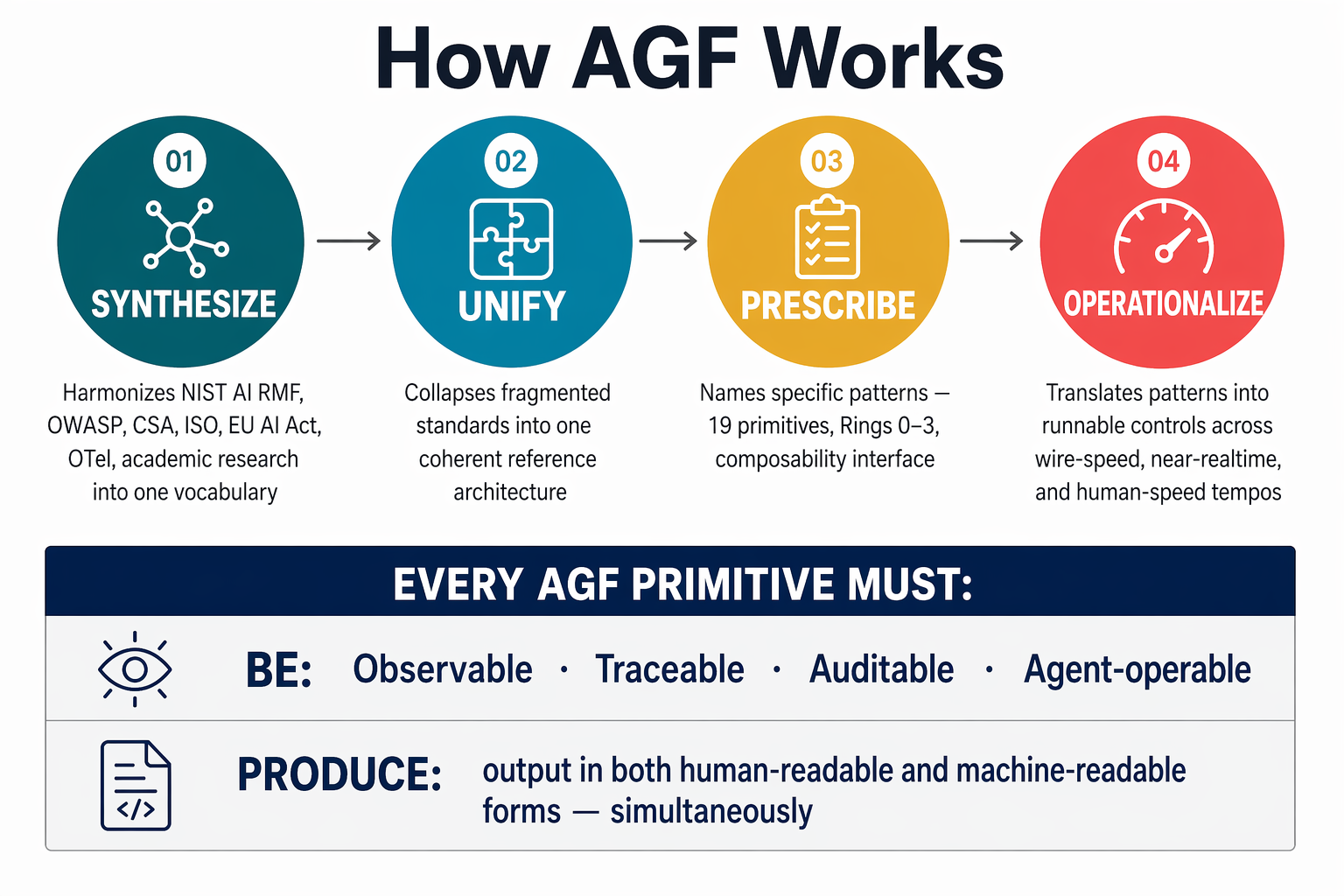
Four-verb causal flow (Synthesize → Unify → Prescribe → Operationalize) plus the two universal requirements every AGF primitive must satisfy: the OTAA invariant (Observable, Traceable, Auditable, Agent-operable) and the dual-form principle.
Reference Architecture — Macro View
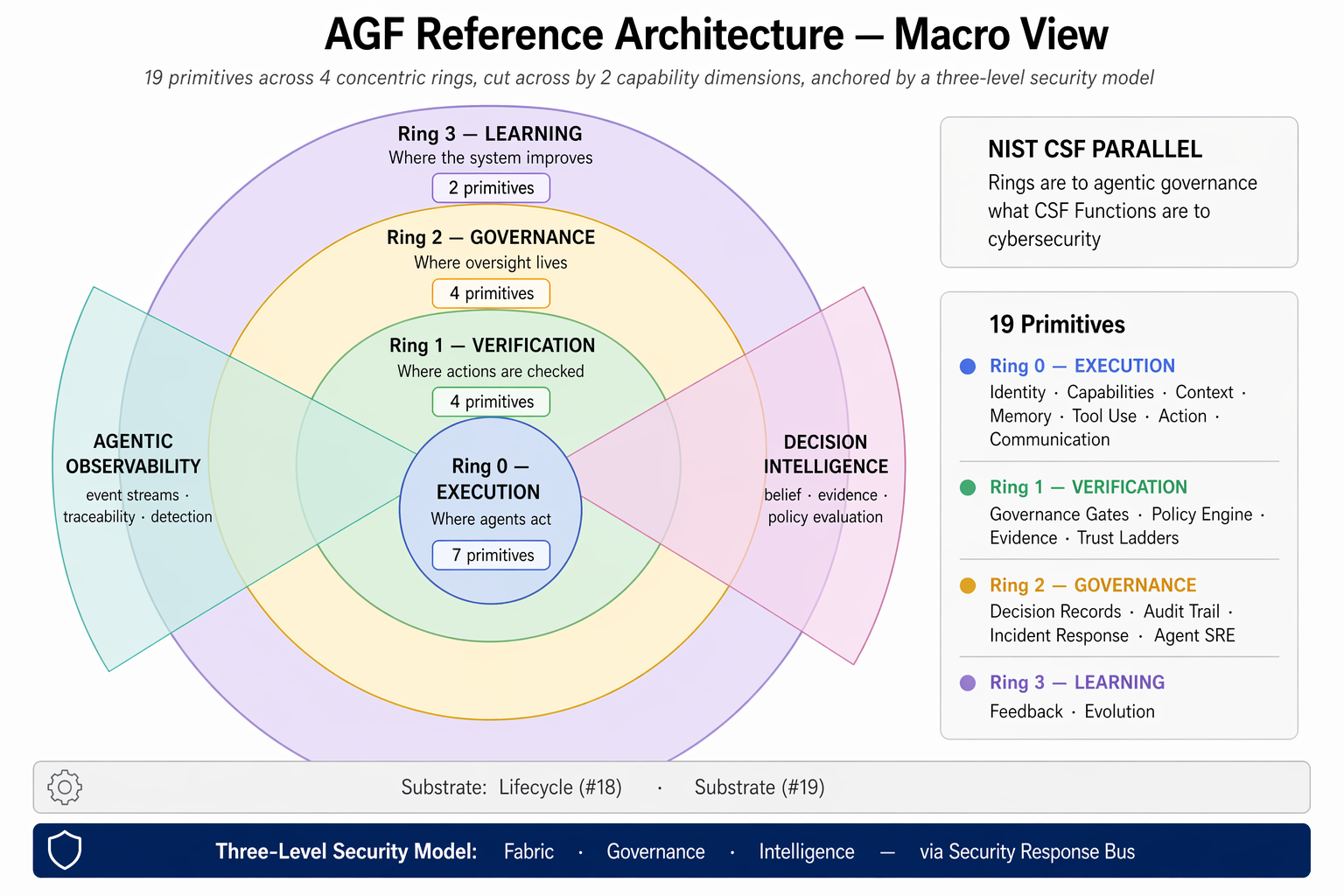
19 primitives across 4 concentric rings, cut through by two cross-cutting capability dimensions (Agentic Observability, Decision Intelligence), anchored by the three-level security model. NIST CSF parallel: rings are to agentic governance what CSF Functions are to cybersecurity.
The Rings Model
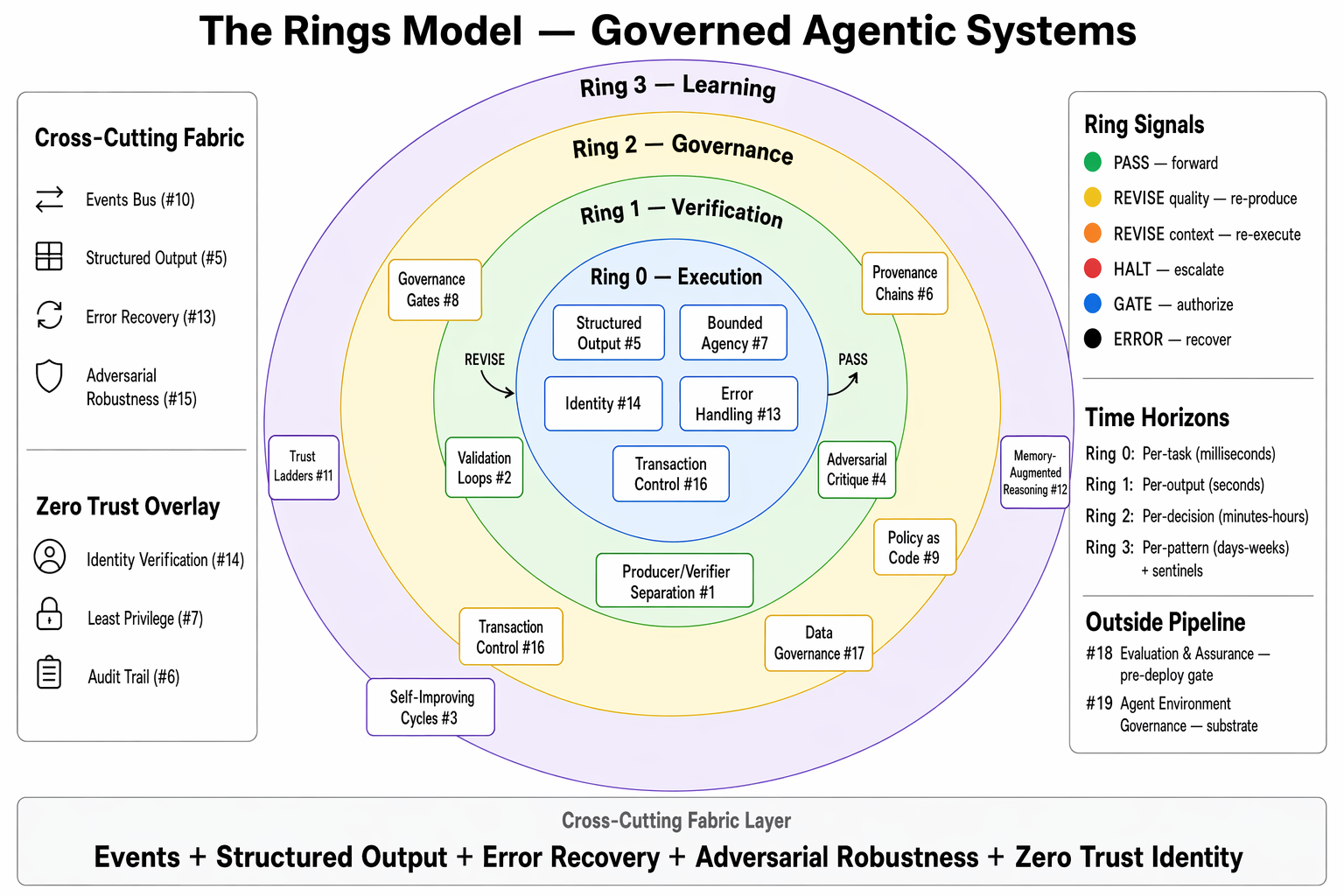
Four concentric rings organizing governance into composable layers, with cross-cutting fabric and environment substrate. Learn more
Ring Deployment Modes
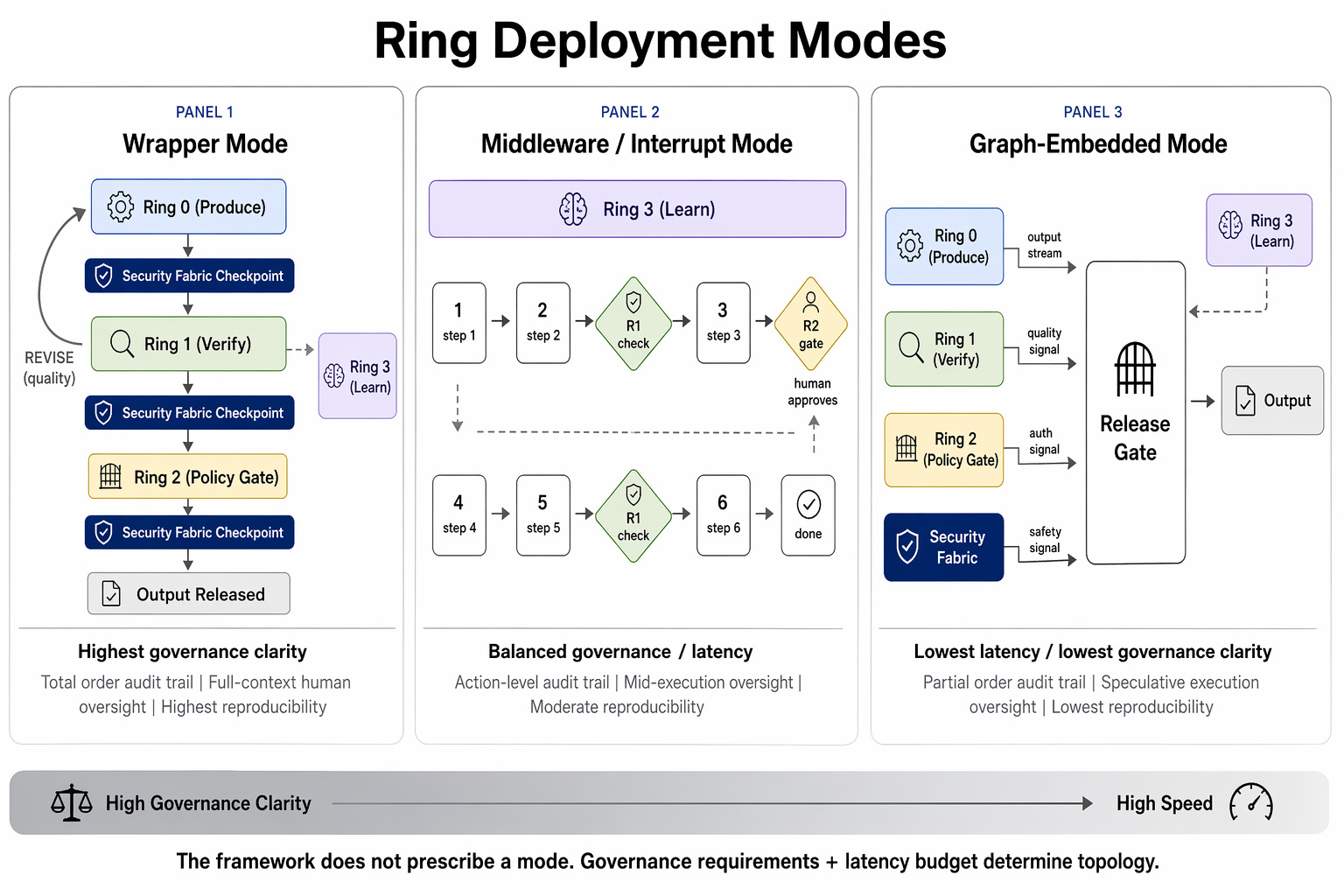
The same logical rings manifest differently depending on system type. Learn more
Three-Level Security Model
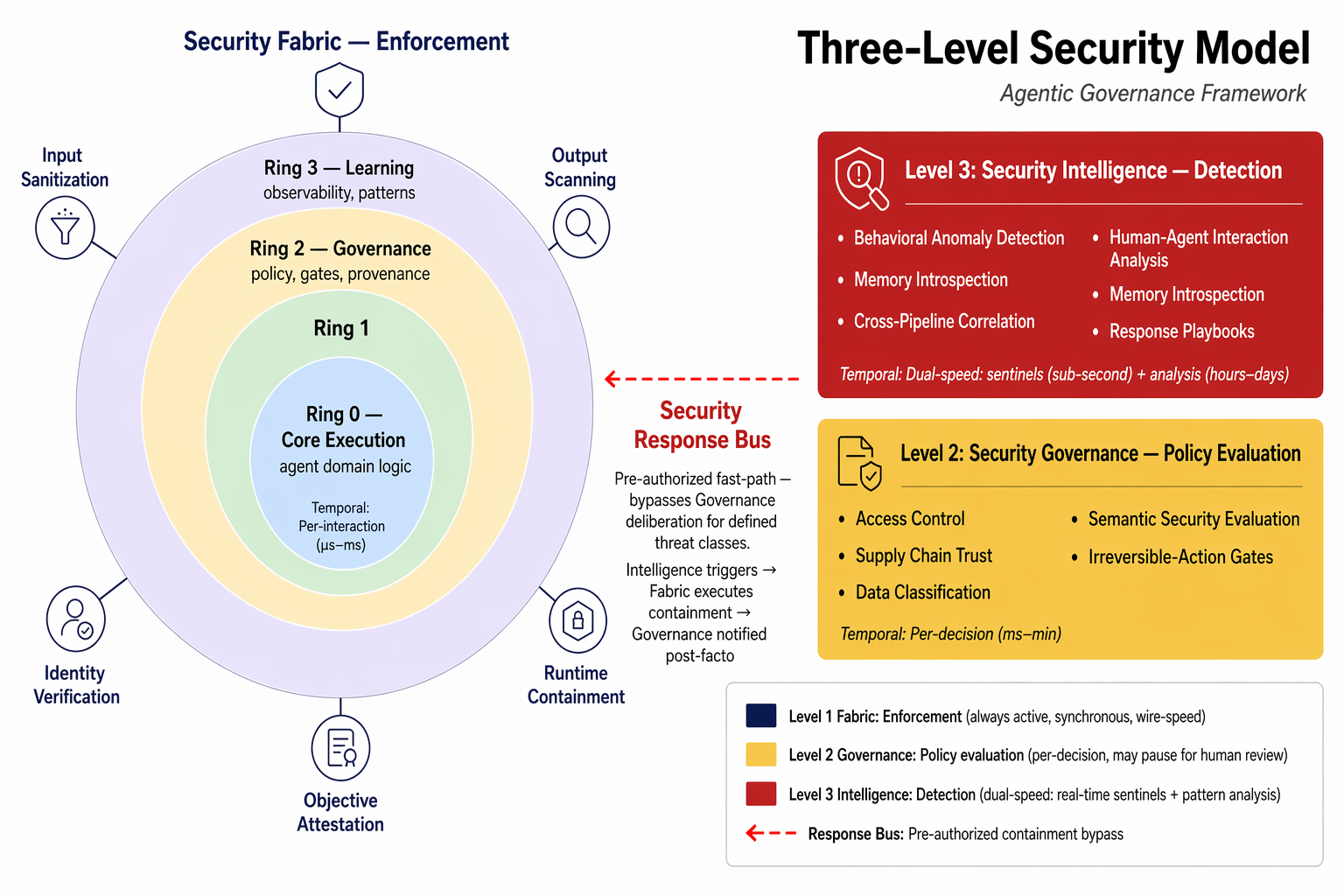
Security as a pervasive concern: Fabric (enforcement), Governance (policy), Intelligence (detection). Learn more
Composition Patterns
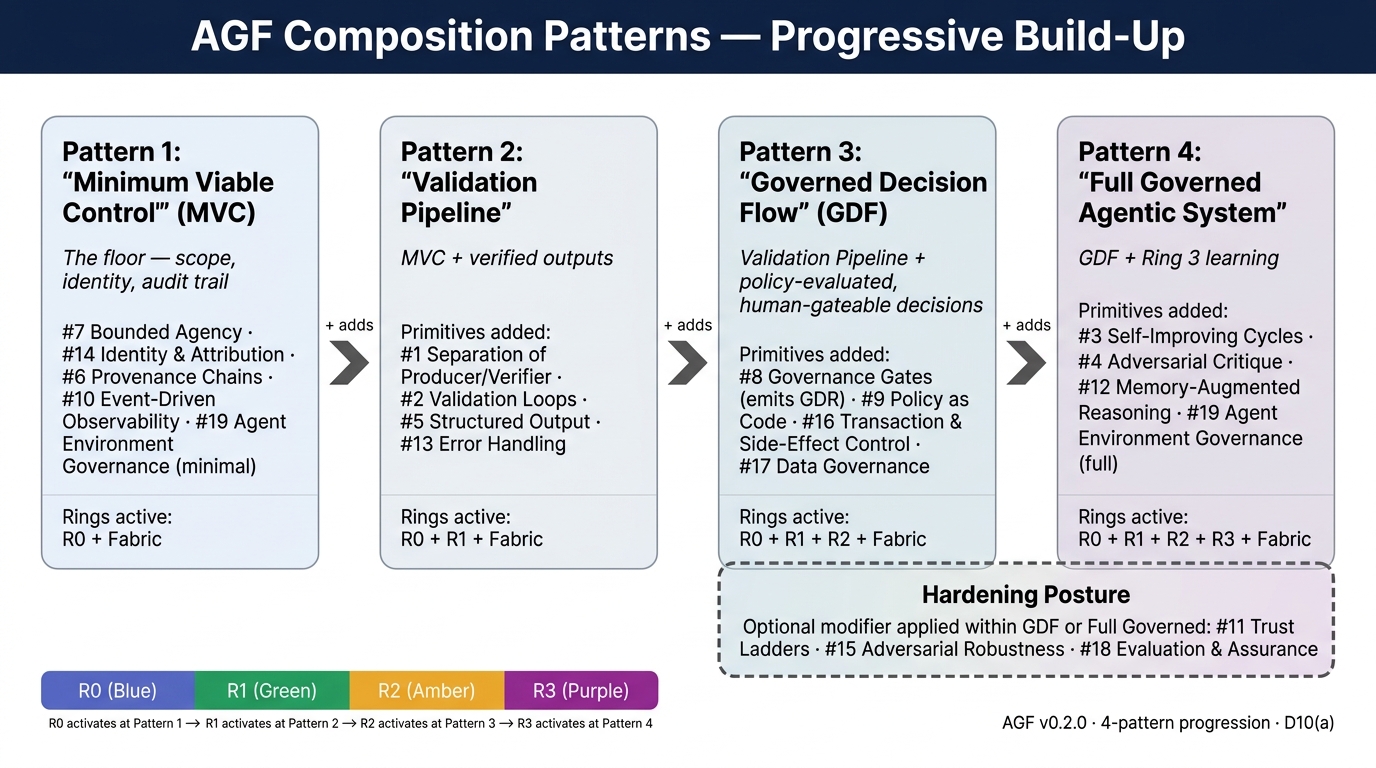
From Minimum Viable Control to Full Governed System. Learn more
Security Response Bus
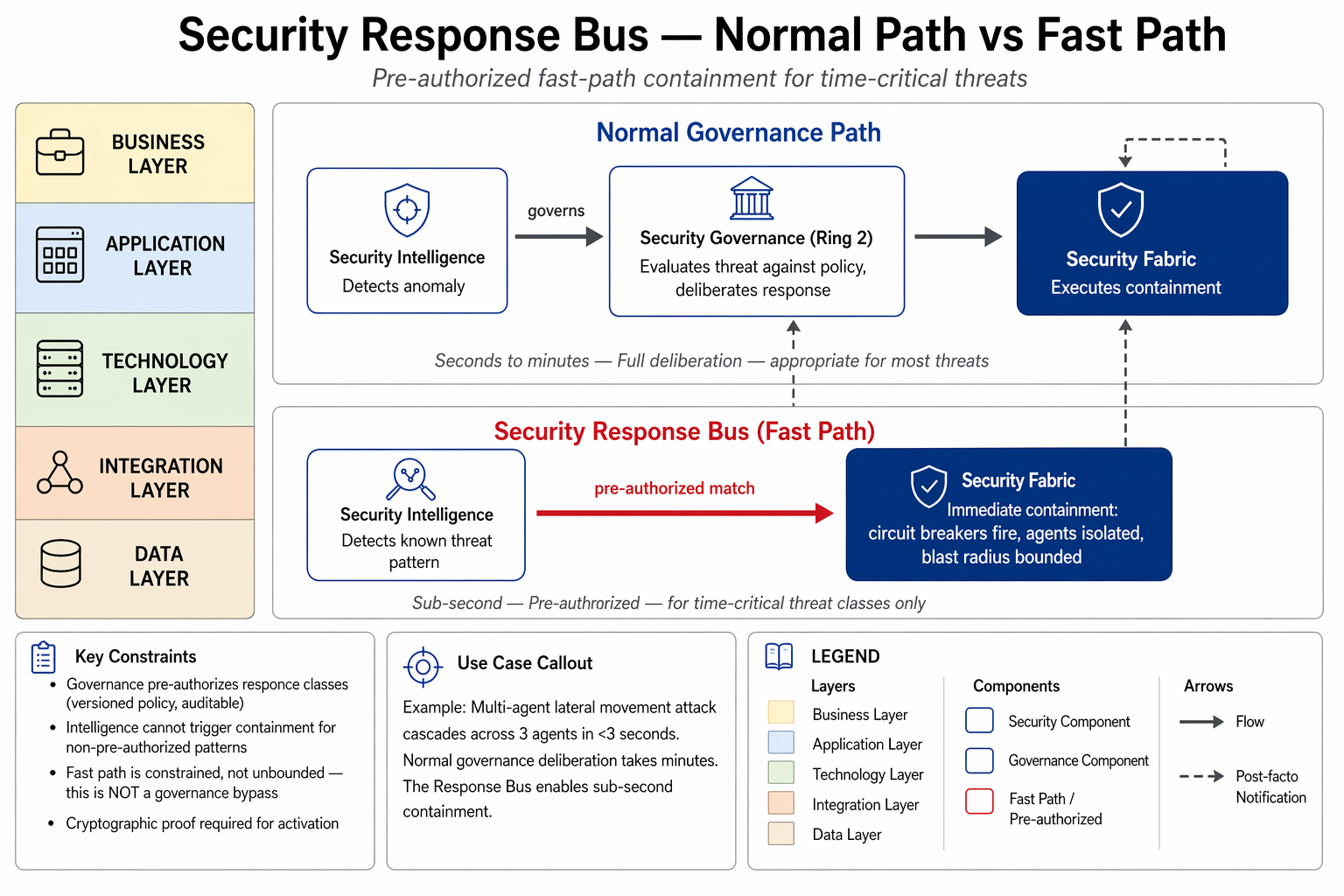
Pre-authorized fast-path from Security Intelligence to Security Fabric, bypassing governance deliberation for defined threat classes.
Event Flow — Observability
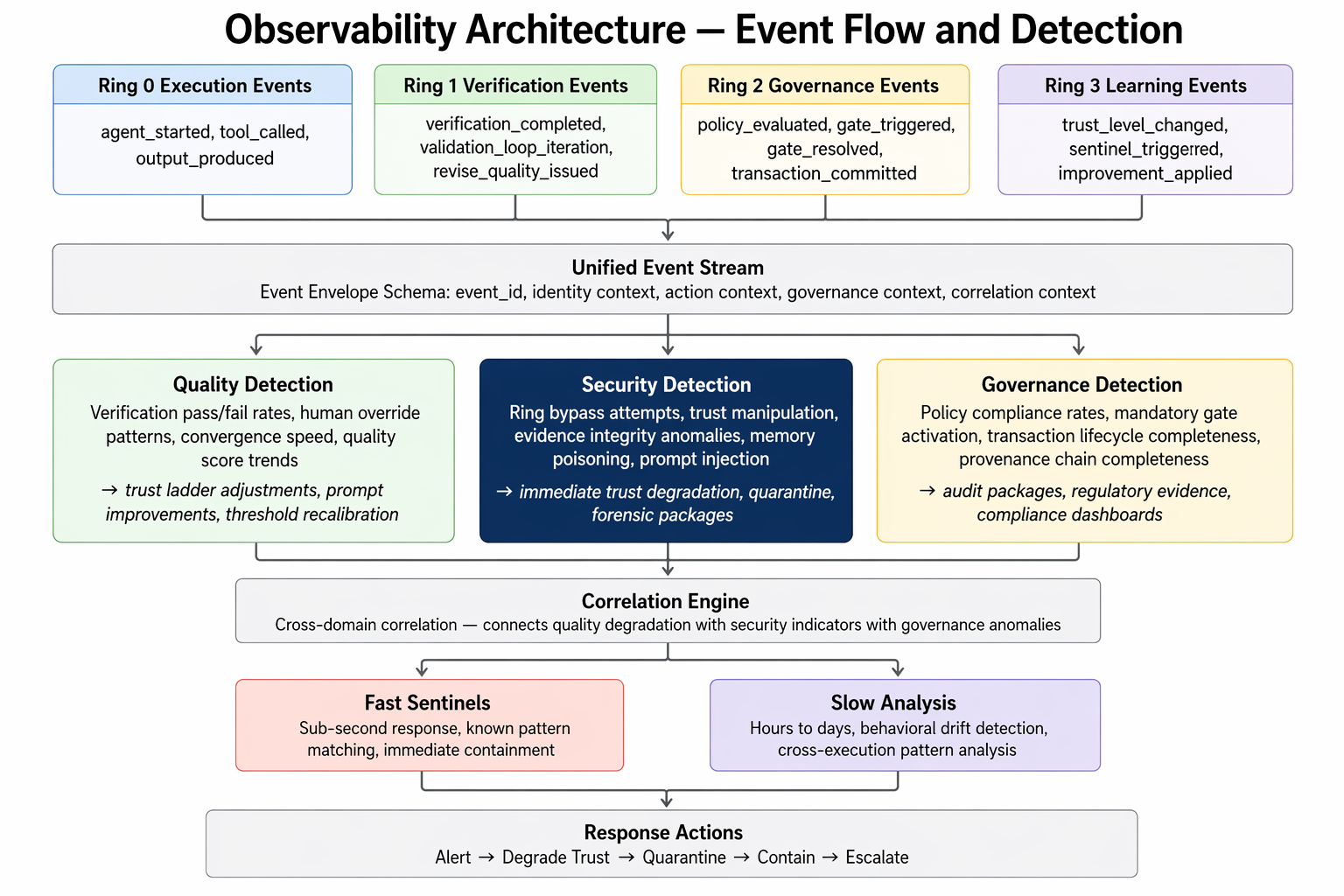
How events flow from ring execution through the correlation engine to the three detection perspectives.
Agent Environment Stack
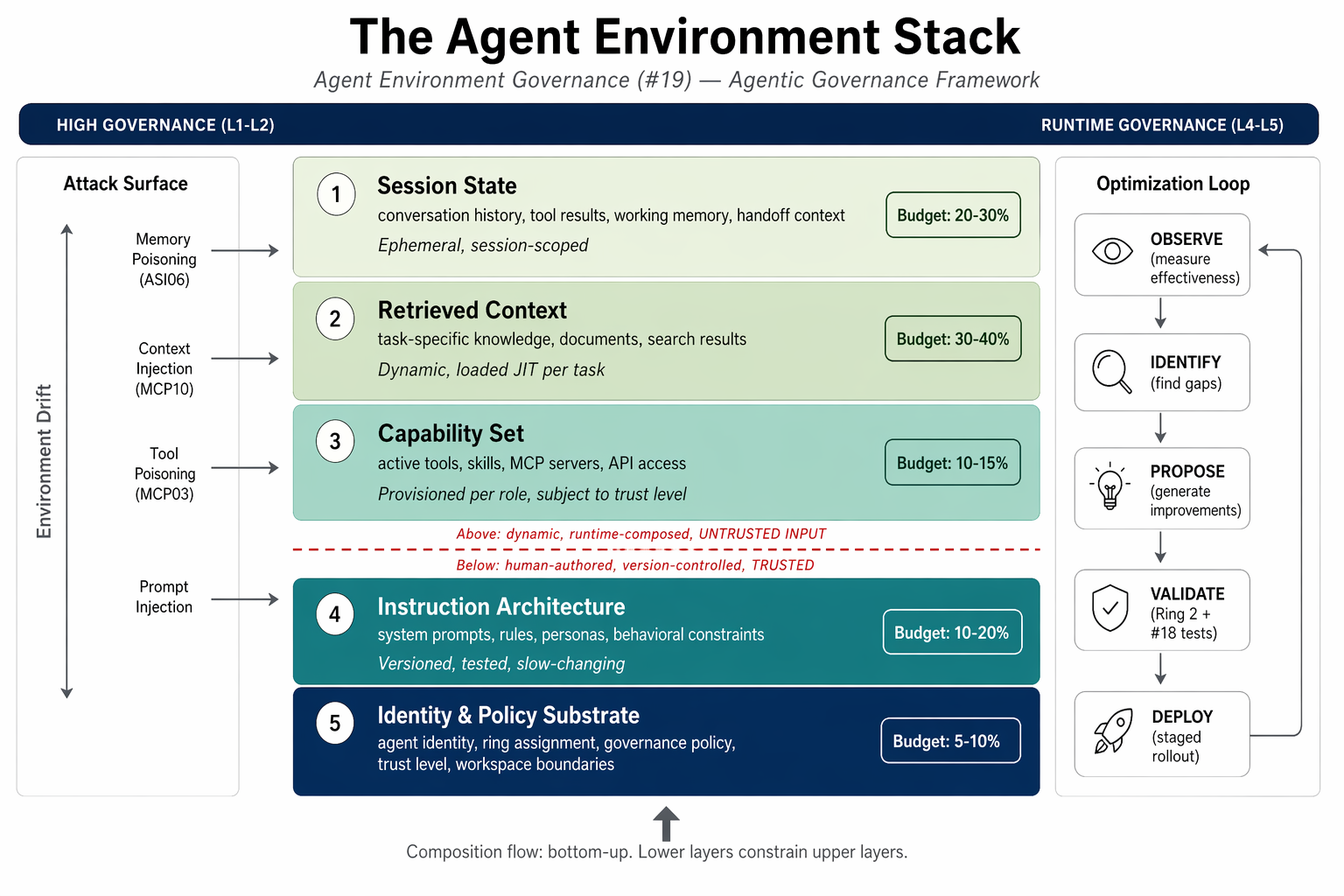
The five layers of the agent operating environment governed by Primitive #19.
Zero Trust Identity Flow
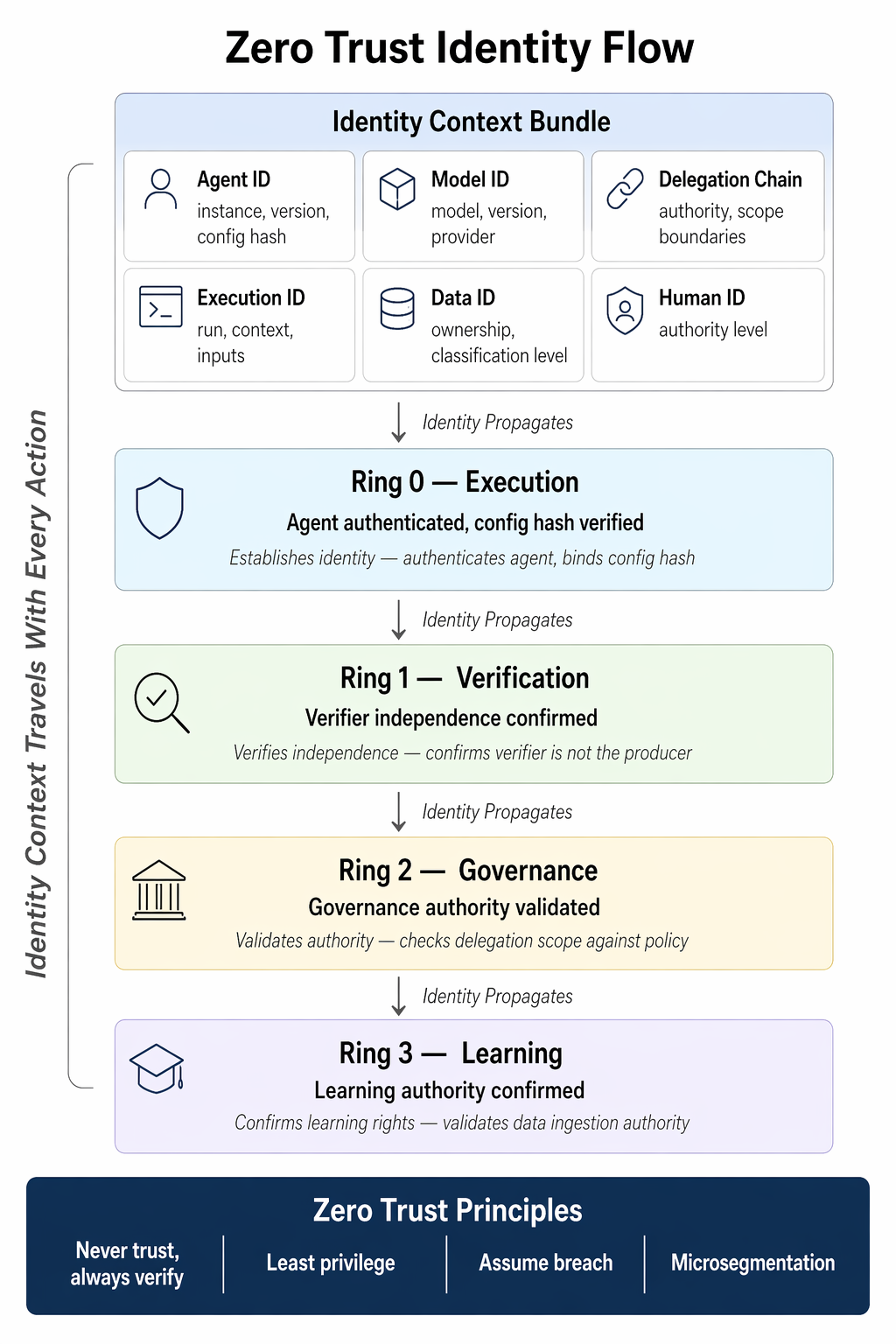
Identity verification at every ring boundary — no implicit trust.