What is AGF?
The Agentic Governance Framework — a synthesis of NIST, OWASP, CSA, EU AI Act, and academic research into a composable reference architecture.
AGF is a reference architecture and operating model for governing agentic systems — synthesizing NIST, OWASP, CSA, ISO, EU AI Act, OpenTelemetry, and academic research into a coherent, composable playbook. It makes agent behavior observable, traceable, auditable, and agent-operable so that the systems shipping today can be governed without rebuilding them tomorrow.
The Problem
Agentic systems are proliferating faster than the architectural patterns to govern them.
Organizations are deploying autonomous agents — coding assistants, ops automation, customer-facing chatbots, decision-support systems, multi-agent workflows — at extraordinary pace. Most deployments today are brittle. They work in demos but fail under scrutiny because they lack the structural primitives that make automated action trustworthy, auditable, and improvable.
The governance landscape is fragmented. NIST provides risk management frameworks. OWASP provides threat taxonomies. CSA provides trust frameworks. ISO provides management systems. OpenTelemetry provides observability standards. The EU AI Act provides regulatory requirements.
Every one of these institutions is doing critical work. These are the dots. The puzzle pieces are on the table.
What AGF Does
AGF connects those dots. We synthesize the best thinking from standards bodies, government frameworks, security organizations, academic researchers, and industry practitioners into a single coherent reference architecture.
We are not claiming to have invented new governance concepts. The patterns — separation of duties, least privilege, audit trails, zero trust, policy as code — are battle-tested across distributed systems, security engineering, compliance, and control theory. The contribution is the composition.
Core Architecture
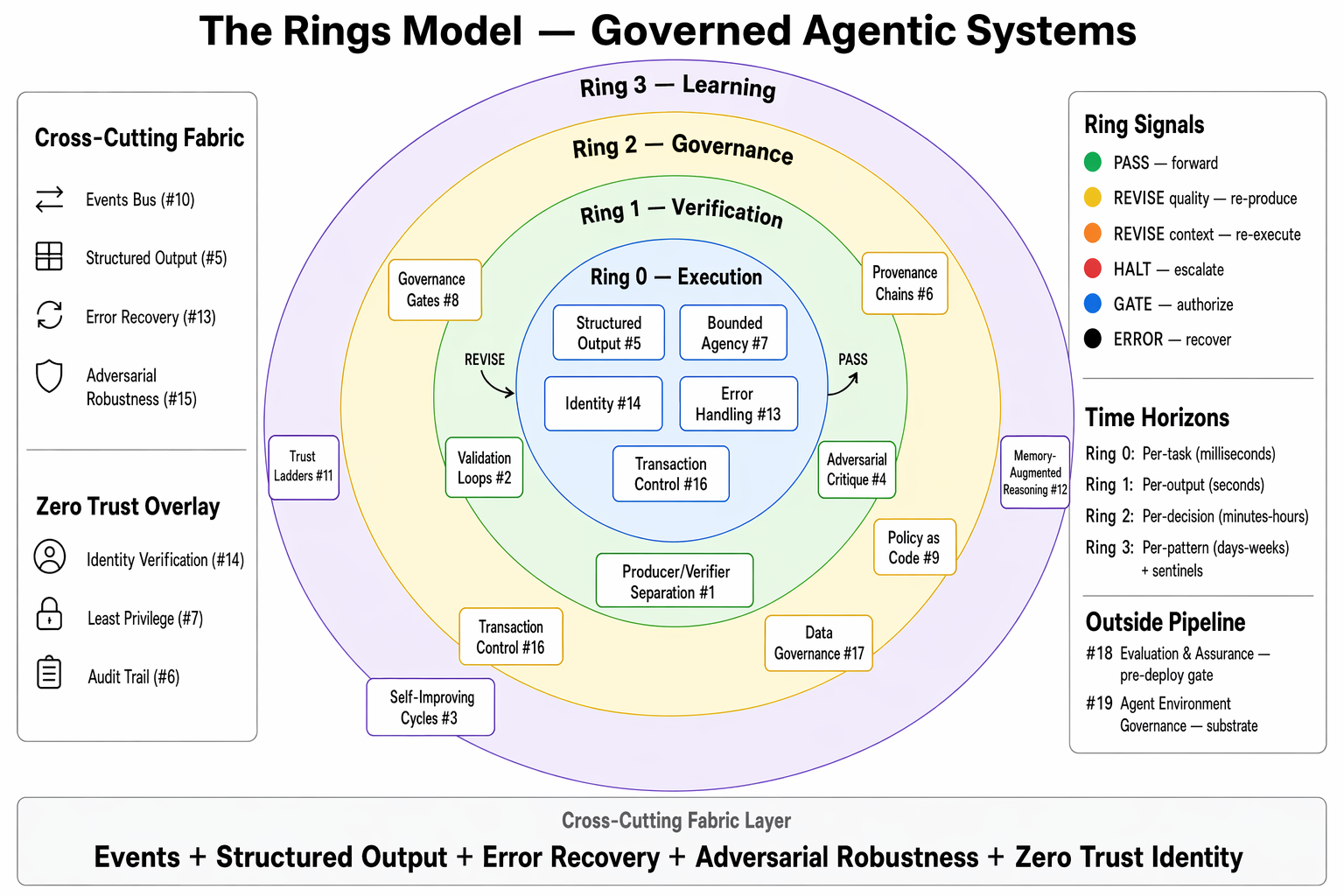
The Rings Model
Four concentric rings organize governance into independent, composable layers:
- Ring 0 — Execution: The agent does its work
- Ring 1 — Verification: A separate process validates the output
- Ring 2 — Governance: Policy evaluation, human gates, authorization
- Ring 3 — Learning: The system improves over time (proposes, never autonomously enacts)
Plus a cross-cutting fabric (events, identity, provenance, error handling) and an environment substrate (governed context, instructions, tools, workspace).
Learn more about the Rings Model →
19 Named Primitives
Nineteen patterns drawn from prior art across distributed systems, security engineering, compliance, and control theory — named for the agentic context. The contribution is the composition, not the patterns.
See the full primitive catalog →
Three-Level Security Model
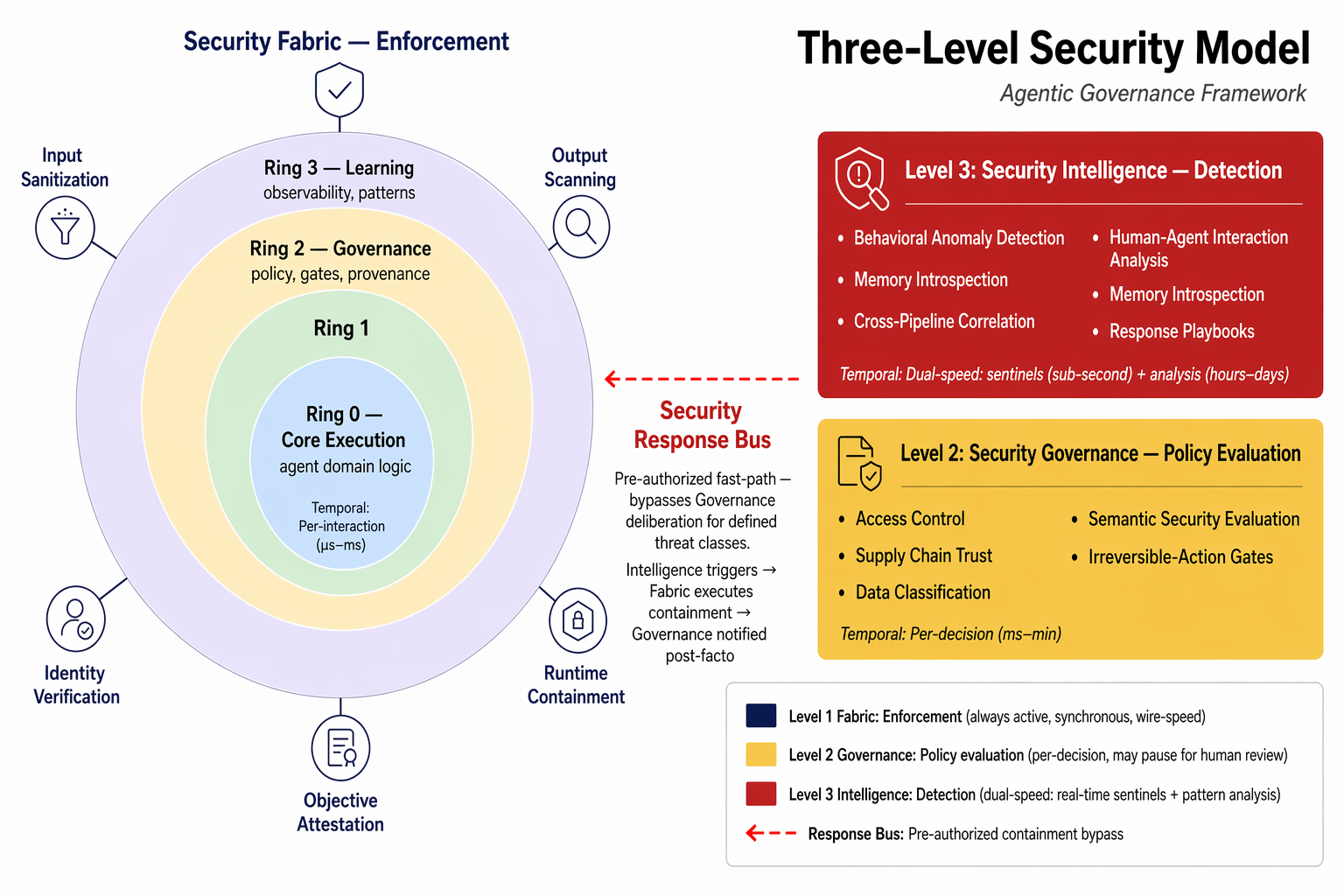
Security is pervasive, not a single layer:
- Level 1: Security Fabric — Enforcement (wire-speed, always active)
- Level 2: Security Governance — Policy evaluation (Ring 2)
- Level 3: Security Intelligence — Detection (SIEM for agents, dual-speed)
See the full security architecture →
Three Deployment Modes
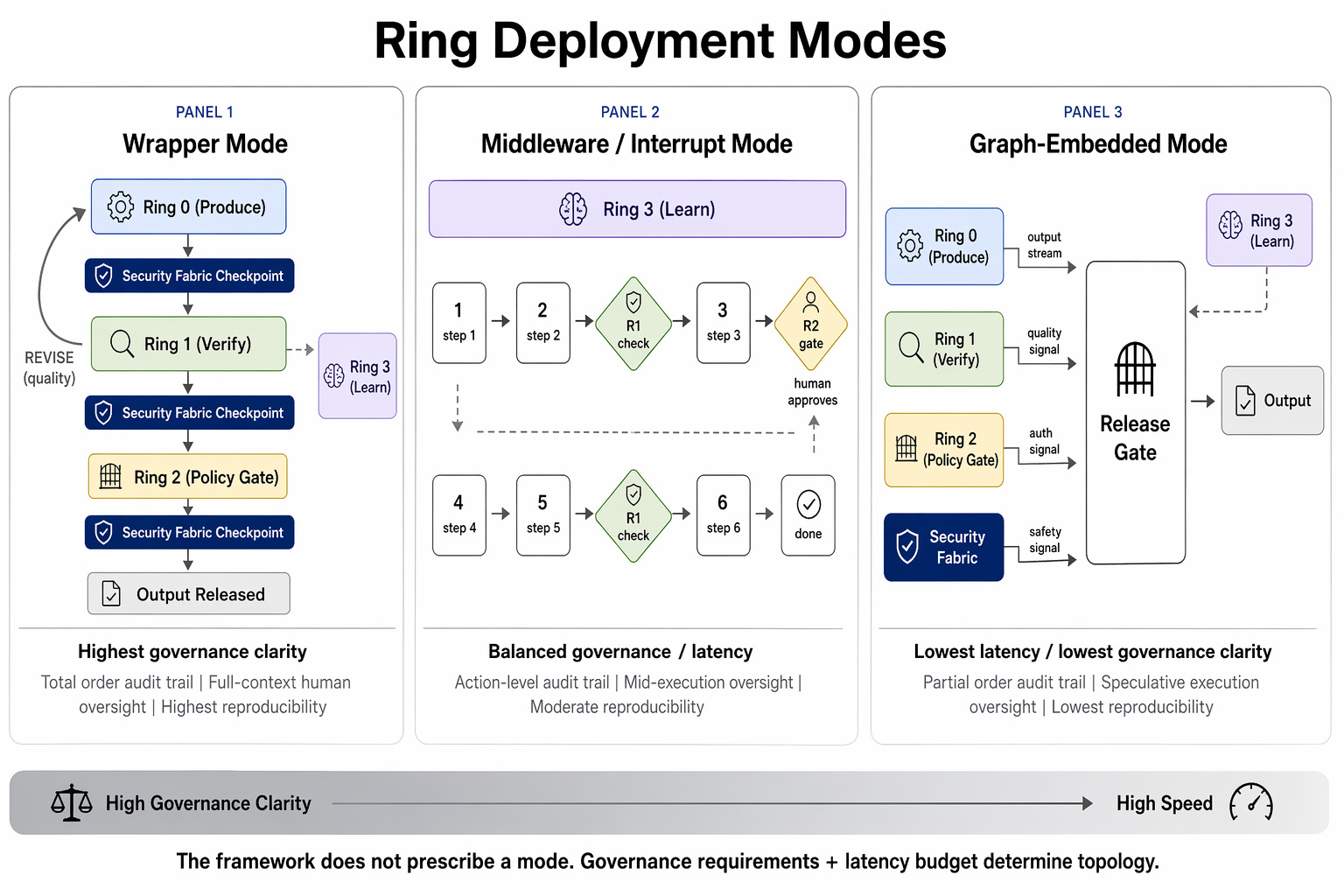
The same logical rings, different physical manifestation:
- Wrapper — sequential, highest audit clarity (batch pipelines)
- Middleware/Interrupt — governance at decision points (coding agents, MCP)
- Graph-Embedded — concurrent, lowest latency (conversational agents)
Standards Alignment
| Standard | AGF Coverage |
|---|---|
| EU AI Act | Article-level mapping (Art. 6, 9-15, 50) with phased applicability |
| NIST AI RMF | AGF as an agentic AI RMF-style profile |
| OWASP ASI Top 10 | All 10 threats mapped to three-level security model |
| OWASP MCP Top 10 | All 10 MCP threats mapped to primitives |
| CSA MAESTRO | 7-layer threat model mapped to primitives |
| MITRE ATLAS | Security architecture aligned to adversarial technique taxonomy |
| NIST 800-53 / ISO 27001 | Control crosswalks in GRC Profile |
Philosophy
AGF synthesizes — it does not decree. Load-bearing empirical and novel claims carry one of three confidence levels so you can audit where AGF stands on the evidence: · · .
Next Steps
- The Rings Model — understand the core architecture
- Trust Ladders — how agents earn autonomy
- Pick your role — five domain profiles, each with the depth your function needs: Security · Platform · GRC · AI Engineering · Observability